From Ingress To Gateway API
Many clusters still rely on the classic kubernetes Ingress, while the Gateway API is becoming the new norm. This blog will talk abount when and how to move, with concrete, operator and app-team perspective.
Target Audience:
1. Platform Engineers.
2. App Team Leads.
I will try to answer these questions:
1. Do you really need to migrate ?
2. Vendor Options Supporting the Kubernetes Gateway API.
3. A low-risk, gradual migration strategy.
Ingress:
- Simple, Layer 7 ( Application Layer) supports only HTTP and HTTPS.
- You will deal with only two types of resources :
- IngressClass (The controller).
- Ingress (The routing rules).
- Widely used and supported.
- Custom annotations for declarative controller enhancement.
- Legacy and forzen.
Gateway API:
If you need to leverage advanced routing capabilities, such as:
- Role separation (GatewayClass)
- Robust, Layer 4 & 7, supports HTTP, HTTPS, TCP, UDP, gRPC.
- Built in cross-namespace support.
- Strong Multi-trnancy. Different team or namespace can define routes differently.
- Actively being developed and furture standard.
- Open Source and Community Projects - NGINX Gateway Fabric, Envoy Gateway HAProxy, Traefik, Contour, Istio, APISIX, etc..
- Cloud Provider - EKS, GKE, AKS, etc..
- Enterprise and API Management Platforms - Kong Gateway, Gloo Gateway (by Solo.io), Tyk, etc..
Ingress2gateway is a prefect tool to do this.
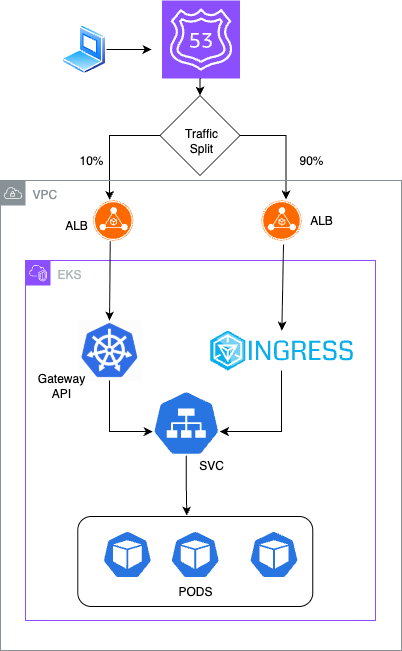
Once that was done, the Gateway API spun up a new ALB, which I then added as a CNAME record in Route 53. To make the migration safer, I decided to create a parallel infrastructure so I could test things using a canary strategy and shift traffic gradually. This setup gave me the flexibility to roll back instantly if anything didn’t go as planned. I used weighted routing in Route 53 to distribute traffic between the old and new environments.
Running a parallel setup does add some temporary cost, but it’s worth it — especially for production or business-critical applications where rollback speed is more important than saving a few dollars. Once the new stack proved stable, I could easily retire the old infrastructure and continue with the new Gateway API–based setup.
Migrating from NGINX Ingress to the Gateway API turned out to be a great opportunity to modernize my traffic management setup on EKS. With Envoy Gateway as the controller, I was able to simplify configuration, gain more flexibility in routing, and align with the future of Kubernetes networking.
Setting up a parallel infrastructure with canary-based DNS routing through Route 53 made the transition seamless and safe, without any downtime. It also gave me the confidence to roll out gradually, observe real-world traffic behavior, and roll back instantly if needed.
If you’re planning a similar migration, I’d recommend:
- Start with a small, non-critical application to get familiar with Gateway API resources.
- Use weighted routing for a controlled traffic shift.
- Keep your rollback path ready until full cutover.